| Exam Name: | Ethical Hacking and Countermeasures V8 | ||
| Exam Code: | EC0-350 Dumps | ||
| Vendor: | ECCouncil | Certification: | Certified Ethical Hacker |
| Questions: | 878 Q&A's | Shared By: | yasmin |
Bob reads an article about how insecure wireless networks can be. He gets approval from his management to implement a policy of not allowing any wireless devices on the network. What other steps does Bob have to take in order to successfully implement this? (Select 2 answer.)
In order to attack a wireless network, you put up an access point and override the signal of the real access point. As users send authentication data, you are able to capture it. What kind of attack is this?
Sally is a network admin for a small company. She was asked to install wireless accesspoints in the building. In looking at the specifications for the access-points, she sees that all of them offer WEP. Which of these are true about WEP?
Select the best answer.
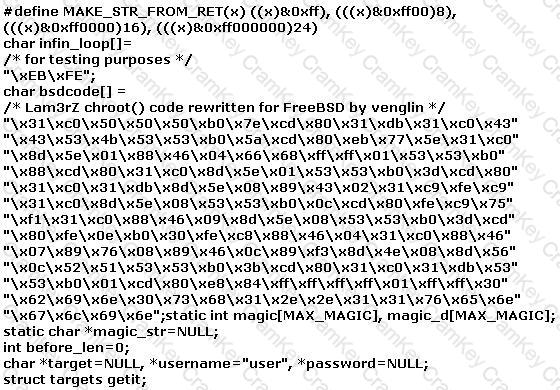
The following exploit code is extracted from what kind of attack?