| Exam Name: | PECB Certified ISO/IEC 27005 Risk Manager | ||
| Exam Code: | ISO-IEC-27005-Risk-Manager Dumps | ||
| Vendor: | PECB | Certification: | ISO/IEC 27005 |
| Questions: | 60 Q&A's | Shared By: | delilah-rose |
Scenario 3: Printary is an American company that offers digital printing services. Creating cost-effective and creative products, the company has been part of the printing industry for more than 30 years. Three years ago, the company started to operate online, providing greater flexibility for its clients. Through the website, clients could find information about all services offered by Printary and order personalized products. However, operating online increased the risk of cyber threats, consequently, impacting the business functions of the company. Thus, along with the decision of creating an online business, the company focused on managing information security risks. Their risk management program was established based on ISO/IEC 27005 guidelines and industry best practices.
Last year, the company considered the integration of an online payment system on its website in order to provide more flexibility and transparency to customers. Printary analyzed various available solutions and selected Pay0, a payment processing solution that allows any company to easily collect payments on their website. Before making the decision, Printary conducted a risk assessment to identify and analyze information security risks associated with the software. The risk assessment process involved three phases: identification, analysis, and evaluation. During risk identification, the company inspected assets, threats, and vulnerabilities. In addition, to identify the information security risks, Printary used a list of the identified events that could negatively affect the achievement of information security objectives. The risk identification phase highlighted two main threats associated with the online payment system: error in use and data corruption After conducting a gap analysis, the company concluded that the existing security controls were sufficient to mitigate the threat of data corruption. However, the user interface of the payment solution was complicated, which could increase the risk associated with user errors, and, as a result, impact data integrity and confidentiality.
Subsequently, the risk identification results were analyzed. The company conducted risk analysis in order to understand the nature of the identified risks. They decided to use a quantitative risk analysis methodology because it would provide more detailed information. The selected risk analysis methodology was consistent with the risk evaluation criteria. Firstly, they used a list of potential incident scenarios to assess their potential impact. In addition, the likelihood of incident scenarios was defined and assessed. Finally, the level of risk was defined as low.
In the end, the level of risk was compared to the risk evaluation and acceptance criteria and was prioritized accordingly.
Based on the scenario above, answer the following question:
What type of risk identification approach did Printary use?
Which statement regarding risks and opportunities is correct?
Scenario 8: Biotide is a pharmaceutical company that produces medication for treating different kinds of diseases. The company was founded in 1997, and since then it has contributed in solving some of the most challenging healthcare issues.
As a pharmaceutical company, Biotide operates in an environment associated with complex risks. As such, the company focuses on risk management strategies that ensure the effective management of risks to develop high-quality medication. With the large amount of sensitive information generated from the company, managing information security risks is certainly an important part of the overall risk management process. Biotide utilizes a publicly available methodology for conducting risk assessment related to information assets. This methodology helps Biotide to perform risk assessment by taking into account its objectives and mission. Following this method, the risk management process is organized into four activity areas, each of them involving a set of activities, as provided below.
1. Activity area 1: The organization determines the criteria against which the effects of a risk occurring can be evaluated. In addition, the impacts of risks are also defined.
2. Activity area 2: The purpose of the second activity area is to create information asset profiles. The organization identifies critical information assets, their owners, as well as the security requirements for those assets. After determining the security requirements, the organization prioritizes them. In addition, the organization identifies the systems that store, transmit, or process information.
3. Activity area 3: The organization identifies the areas of concern which initiates the risk identification process. In addition, the organization analyzes and determines the probability of the occurrence of possible threat scenarios.
4. Activity area 4: The organization identifies and evaluates the risks. In addition, the criteria specified in activity area 1 is reviewed and the consequences of the areas of concerns are evaluated. Lastly, the level of identified risks is determined.
The table below provides an example of how Biotide assesses the risks related to its information assets following this methodology:
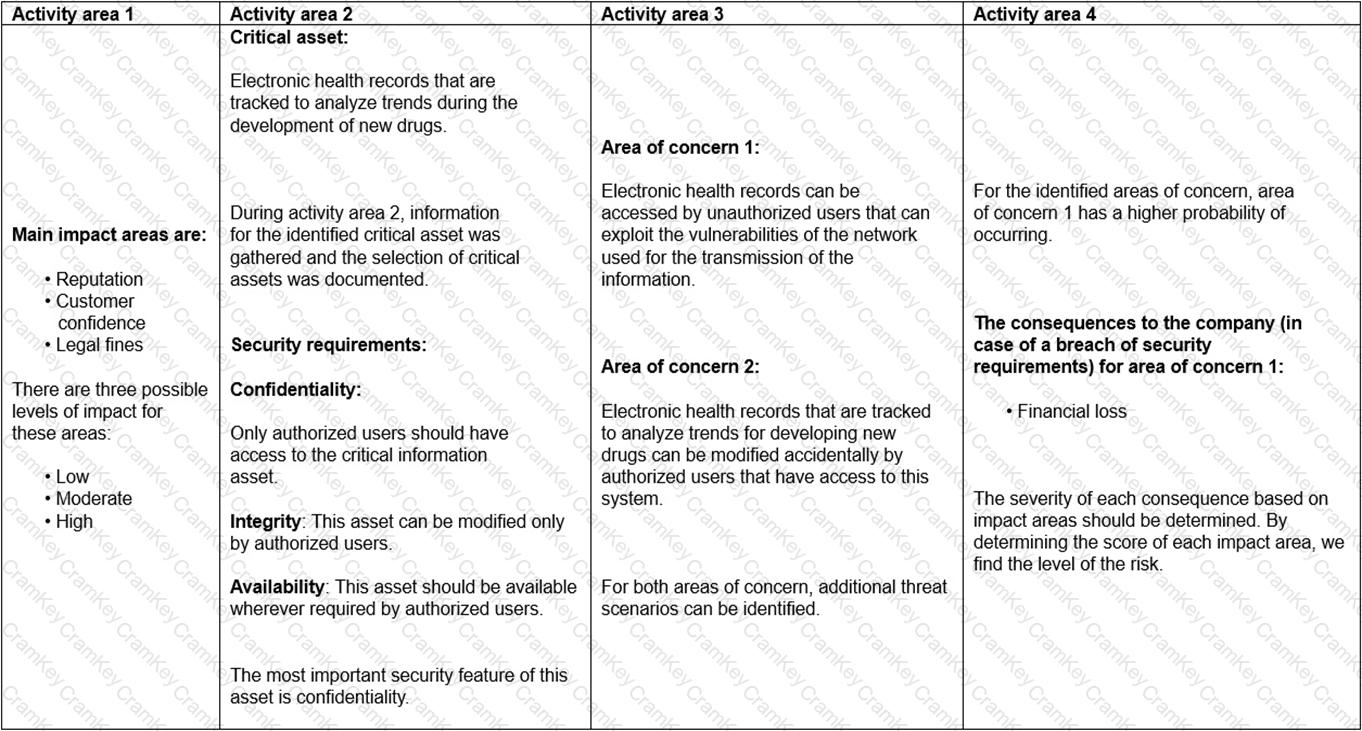
Based on the table provided in scenario 8, did Biotide prioritize the security requirements for electronic health records?