| Exam Name: | Implementing and Operating Cisco Security Core Technologies (SCOR 350-701) | ||
| Exam Code: | 350-701 Dumps | ||
| Vendor: | Cisco | Certification: | CCNP Security |
| Questions: | 630 Q&A's | Shared By: | crystal |
Refer to the exhibit.
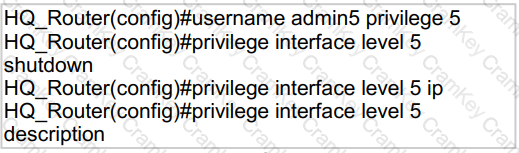
A network administrator configures command authorization for the admin5 user. What is the admin5 user able to do on HQ_Router after this configuration?
Which license is required for Cisco Security Intelligence to work on the Cisco Next Generation Intrusion
Prevention System?
How is ICMP used an exfiltration technique?