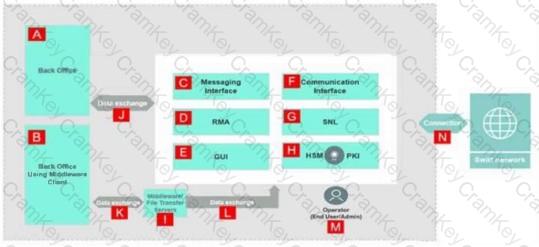
The Swift Customer Security Controls Framework (CSCF) defines the scope of components that must comply with its security controls. This scope is detailed in theCSCF v2024(and prior versions like CSCF v2023), which specifies that the CSCF applies to systems directly involved in the Swift messaging and connectivity ecosystem. Let’s analyze the diagram to identify which components fall within this scope.
Step 1: Understand the Scope of CSCF
According to theSwift Customer Security Controls Framework (CSCF) v2024, the scope includes:
Swift messaging interfaces(e.g., Alliance Access/Entry, RMA).
Communication interfacesto the Swift network (e.g., SNL, HSM, PKI).
Operator systemsdirectly interacting with Swift components (e.g., GUIs, admin/operator workstations).
Middlewareor connectors directly facilitating Swift message flows.Systems that are not directly involved in Swift messaging or connectivity (e.g., back-office systems, general-purpose servers) are typically out of scope unless they pose a direct risk to the Swift environment.
Step 2: Analyze the Diagram and Identify Components
The diagram includes the following labeled components:
A. Back Office: A system for back-office operations, not directly part of Swift messaging.
B. Back Office Using Middleware Client: A back-office system with middleware for data exchange.
C. Messaging Interface: Likely a Swift messaging interface (e.g., Alliance Access).
D. RMA: Relationship Management Application, a Swift component for managing messaging relationships.
E. GUI: Graphical User Interface for operators to interact with the messaging interface.
F. Communication Interface: Interface for connecting to the Swift network.
G. SNL: SwiftNet Link, a communication layer for Swift connectivity.
H. HSM & PKI: Hardware Security Module and Public Key Infrastructure, used for secure Swift connectivity.
I. Middleware File Transfer Servers: Servers facilitating data exchange between back-office and Swift systems.
J, K, L. Data Exchange Paths: Represent data flows between systems (not components themselves).
M. Operator (End User): The operator’s workstation interacting with the Swift GUI.
N. Connector: The connection point to the Swift network.
Step 3: Evaluate Each Option Against CSCF Scope
A. Components A, B, K
A (Back Office): Back-office systems are not in scope unless they directly process Swift messages. The CSCF focuses on Swift-specific infrastructure, and back-office systems are typically considered out of scope unless they pose a direct risk (e.g., via middleware).
B (Back Office Using Middleware Client): While this system uses middleware to exchange data with Swift components, it is still a back-office system, not a core Swift component. The middleware itself (I) may be in scope, but the client (B) is not.
K (Data Exchange Path): This is a data flow, not a component, and thus not directly in scope.Conclusion: This option is incorrect.
B. Components J, K, I
J, K (Data Exchange Paths): These are data flows, not components, and are not directly in scope.
I (Middleware File Transfer Servers): Middleware that facilitates Swift message flows (e.g., between back-office and messaging interface) can be in scope if it directlyprocesses or transmits Swift messages. PerControl 1.1: Swift Environment Protection, middleware in the Swift data flow must be secured, making it in scope. However, this option pairs I with J and K, which are not components.Conclusion: This option is incorrect due to J and K, though I alone would be in scope.
C. Components F, G, H
F (Communication Interface): This is the interface connecting to the Swift network, clearly in scope perControl 1.1.
G (SNL): SwiftNet Link is a core communication component for Swift connectivity, in scope perControl 1.1.
H (HSM & PKI): HSM and PKI are critical for secure Swift connectivity, in scope perControl 1.1.Conclusion: This option is correct.
D. Components C, E, M
C (Messaging Interface): This is a core Swift component (e.g., Alliance Access), in scope perControl 1.1.
E (GUI): The GUI used by operators to interact with the messaging interface is in scope, as specified inControl 1.2: Logical Access Control, which includes operator systems.
M (Operator End User): The operator’s workstation is in scope as it directly interacts with Swift systems, perControl 1.2.Conclusion: This option is correct.
Step 4: Conclusion and Verification
The components in scope of the CSCF are those directly involved in Swift messaging, connectivity, and operator interaction. Based on the analysis:
C (F, G, H)includes communication components, all in scope.
D (C, E, M)includes the messaging interface, GUI, and operator workstation, all in scope.Components A, B, and data exchange paths (J, K, L) are not directly in scope, though middleware (I) would be if considered separately.
References
Swift Customer Security Controls Framework (CSCF) v2024, Control 1.1: Swift Environment Protection.
Swift Customer Security Programme – Scope and Applicability, Section: CSCF Scope Definition.
CSCF v2024, Control 1.2: Logical Access Control.